Blockchains are so reliable that they have become prevalent among systems that involve transactions. Therefore, we’ll introduce what blockchains are and how they work in this article.
How Do Blockchains Work?
A blockchain is a distributed and decentralized database made of data points (known as blocks) chained together. Each block contains the data, its own hash, and the hash of the previous block. Keep in mind that a hash is a one-way mathematical function that produces a value with a fixed length from an arbitrary input string. Therefore, if anything has changed inside the data point, its hash will also change, enabling the system to identify problematic blocks.
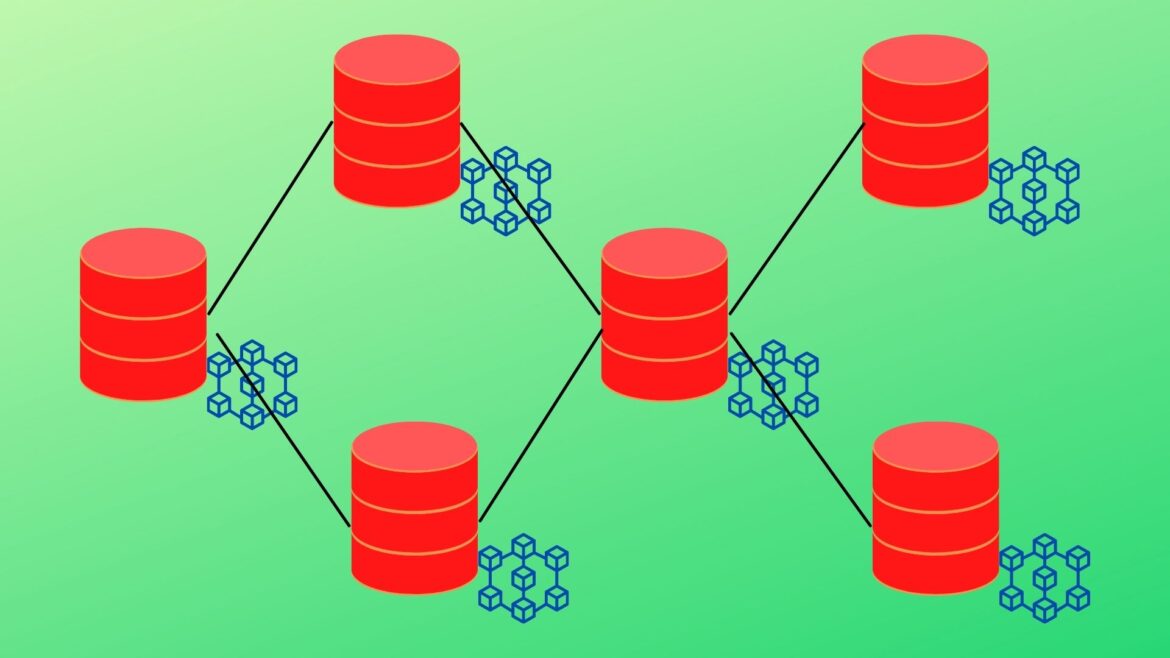
Moreover, blockchains emphasize redundancy instead of being managed by only one central server. Many servers get hold of a copy of the whole blockchain so that no one can make the decision on their own. Instead, the entire group decides on what is valid or invalid. If one block has the same value in most servers, that common value will be considered the correct piece of information contained in the data point.
Once a transaction is made in a blockchain-powered system, a block representing this transaction will be created and sent to every node of the system network. After that, the computers need to resolve the transaction using complex mathematical functions, and the block is then added to the blockchain.
How Hard is it to Hack a Blockchain?
Blockchains are designed to be tedious to modify so that the data will be reliable and original. However, there are still ways to hack them, though they are more complicated than hacking a centralized server.
To illegally manipulate the data in a blockchain, hackers must first find one or more vulnerabilities that cover over 50% of the nodes involved in the blockchain. Secondly, attackers must design backdoors to sneak into those servers to change the data inside. This is known as a 51% attack because once the hackers have control over more than half of the related servers, it becomes possible for the blockchain to validate the wrong value or add new transactions that aren’t supposed to exist.
Nevertheless, blockchains are far more secure than centralized systems, thus are used by most cryptocurrencies to manage transactions.
Conclusion
In this article, we talked about how blockchains are designed to be robust, how to add a transaction to a blockchain, and a type of cyberattack that exploits the weaknesses of blockchains. If you want to learn more about these systems, take a look at the webpages in the references below.
References and Credits
- Adam Hayes, Julius Mansa. (n.d.). Blockchain Explained. Retrieved December 26, 2021, from https://www.investopedia.com/terms/b/blockchain.asp
- Simply Explained. (2017, November 14). How does a blockchain work – Simply Explained. Retrieved December 26, 2021, from https://www.youtube.com/watch?v=SSo_EIwHSd4
- Michele D. Aliessi. (2016, June 2). How Does the Blockchain Work? Retrieved December 26, 2021, from https://onezero.medium.com/how-does-the-blockchain-work-98c8cd01d2ae
- (n.d.). What Is Blockchain Technology? How Does It Work? Retrieved December 26, 2021, from https://builtin.com/blockchain
- Kinza Yasar. (2021, May 29). Is It Possible to Hack the Blockchain? Retrieved December 26, 2021, from https://www.makeuseof.com/is-it-possible-to-hack-the-blockchain/